SETTING UP A VPN SYSTEM IN A LINUX SERVER: 8 IMPORTANT TIPS THAT WILL KEEP YOU SAFE
- Category : Server Administration
- Posted on : Feb 26, 2017
- Views : 2,855
- By : Hagen V.
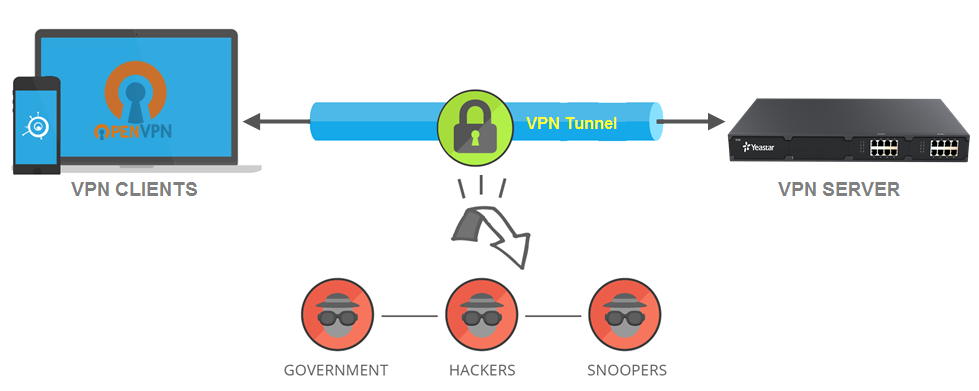
Although internet connections are readily available and cheap these days, not all of them are secure. A Virtual Private Network (VPN) enables you to create a secure network in your home or organization within a Wi-Fi or internet connection that seems insecure. Today, there are different platforms on which you can set up a VPN. However, a Linux server, particularly Ubuntu, is the best option. Nevertheless, no system is 100% secure.
Here are 8 tips on how to enhance security when setting up a VPN system on a Linux server:
- Create certificates
An OpenVPN server relies on certificate authority. As a client, you need certificates to authenticate to your server. Creating these certificates is a process with three basic steps.
These are:
- cd/etc/openvpn/easy-rsa/
- source vars
- ./pkitool hostname
The hostname, in this case, is the name of the machine that will be used to connect to VPN. Essentially, you should create certificates for all machines that will connect to your VPN. After creating the certificates, copy them to respective clients.
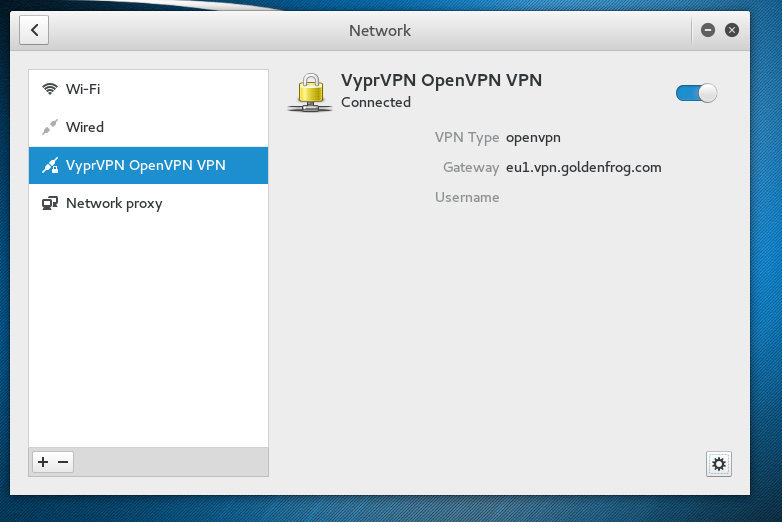
- Use a strong authentication method for your VPN access
The authentication method options that you have depend on the network infrastructure. It’s therefore important that you check with your provider to determine what options you have. With Linux servers, you have an option to enter your credentials. Essentially, you will be prompted to enter your VPN password or username. These are the credentials that you get when signing up for a VPN service. Keep them secure to avoid unauthorized access to your network.

3 .Limit access to people with valid reasons only
VPN is like a door to LAN. Therefore, it should be opened to the right people at the right time only. In fact, you should allow access to selected files of your VPN. A secure HTTPS or secure HTTP website will expose selected files only if you have a strong authentication measure in place. Thus, by limiting access to your VPN, you will avoid risking your entire network.
4. Create an Authentication Key-pair
Create a 4096-bit RSA key-pair from a local computer. While creating this key-pair, you will get an option to encrypt your private key using a passphrase. That means nobody can use it without entering this passphrase unless it is saved to the keychain manager of a local desktop. It’s highly recommended that you use a key-pair and passphrase despite the fact that you have an option to leave the field blank.
5. Remove the unused network
A Linux distribution can install even when there is a running network service. Unfortunately, some network services listen to the incoming internet connection, loopback interface, or even both. Therefore, to reduce attack surface for both the installed packages and the running processes, remove network-facing services that you don’t need. By running “sudo ss –lnp”, you will see the running services. To remove them, run “sudo apt purge package_name”.
6. Use security extensions
Linux provides different security patches. Use them to guard your VPN against compromised or mis-configured programs. If possible, use Linux security extensions like SELinux to enforcing programs and network limitations. For instance, SELinux provides different Linux kernel security policies.
7. Keep software and the Linux Kernel up to date
Security patches’ application is very important in Linux server maintenance. Linux provides the necessary tools for keeping a system updated. It also allows easy upgrade of Linux versions. Therefore, make sure you apply security updates immediately.
8. Forbid the use of other networks while connected to your VPN
You don’t want to expose your VPN to other networks. In most VPN software, routing for clients is set to use the default gateway of the network after connection. However, this is optional. As such, many people find browsing when operating from remote locations prohibitively slow if all traffic routes via the network. Therefore, they opt to turn off this option. Unfortunately, this defeats protection against hostile sites that have been established at the gateway or proxy. To deal with this issue, install a proxy firewall to allow employees or users to access the network from remote locations safely without slowing down their internet connection.
Maintaining VPN security requires vigilance. Follow these tips when setting up a VPN system on a Linux server and you will avoid VPN-related security breaches.
Categories
Subscribe Now
10,000 successful online businessmen like to have our content directly delivered to their inbox. Subscribe to our newsletter!Archive Calendar
| Sat | Sun | Mon | Tue | Wed | Thu | Fri |
|---|---|---|---|---|---|---|
| 1 | ||||||
| 2 | 3 | 4 | 5 | 6 | 7 | 8 |
| 9 | 10 | 11 | 12 | 13 | 14 | 15 |
| 16 | 17 | 18 | 19 | 20 | 21 | 22 |
| 23 | 24 | 25 | 26 | 27 | 28 | 29 |
| 30 | 31 | |||||
Recent Articles
-

Posted on : Jul 25
-

Posted on : Jul 07
-

Posted on : Apr 07
-

Posted on : Mar 19
Optimized my.cnf configuration for MySQL 8 (on cPanel/WHM servers)
Tags
- layer 7
- tweak
- kill
- process
- sql
- Knowledge
- vpn
- seo vpn
- wireguard
- webmail
- ddos mitigation
- attack
- ddos
- DMARC
- server load
- Development
- nginx
- php-fpm
- cheap vpn
- Hosting Security
- xampp
- Plesk
- cpulimit
- VPS Hosting
- smtp
- smtp relay
- exim
- Comparison
- cpu
- WHM
- mariadb
- encryption
- sysstat
- optimize
- Link Building
- apache
- centos
- Small Business
- VPS
- Error
- SSD Hosting
- Networking
- optimization
- DNS
- mysql
- ubuntu
- Linux